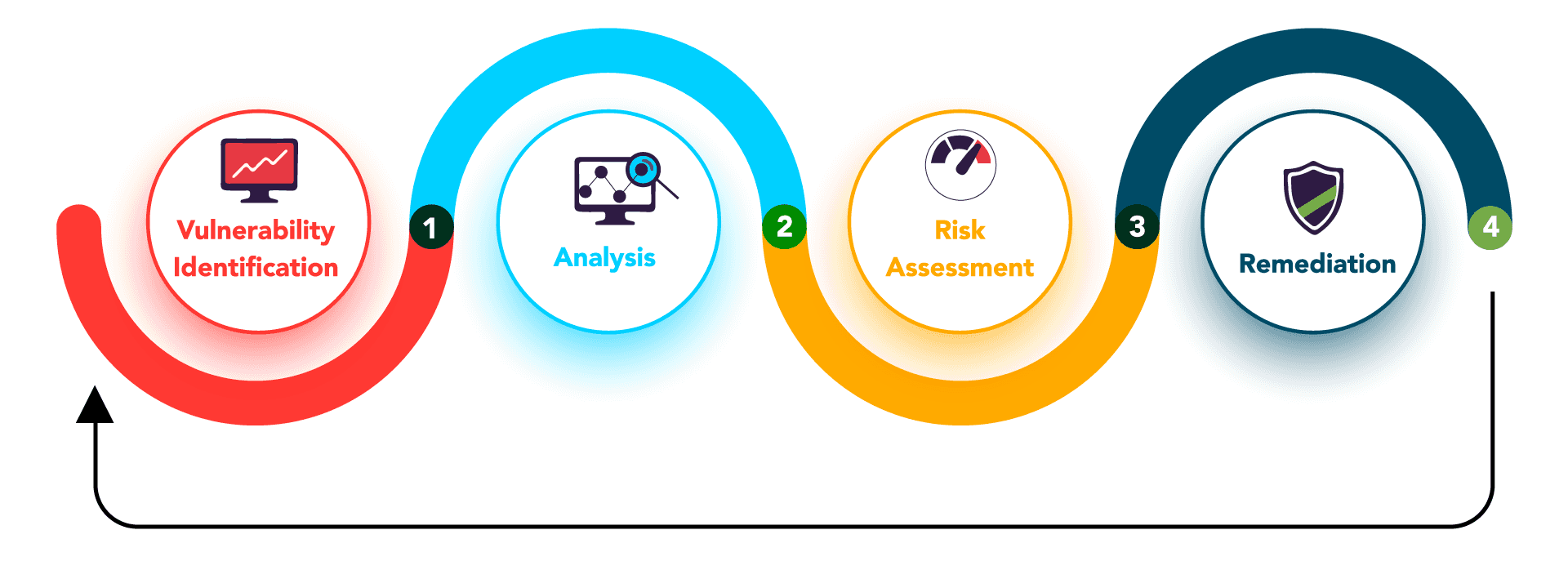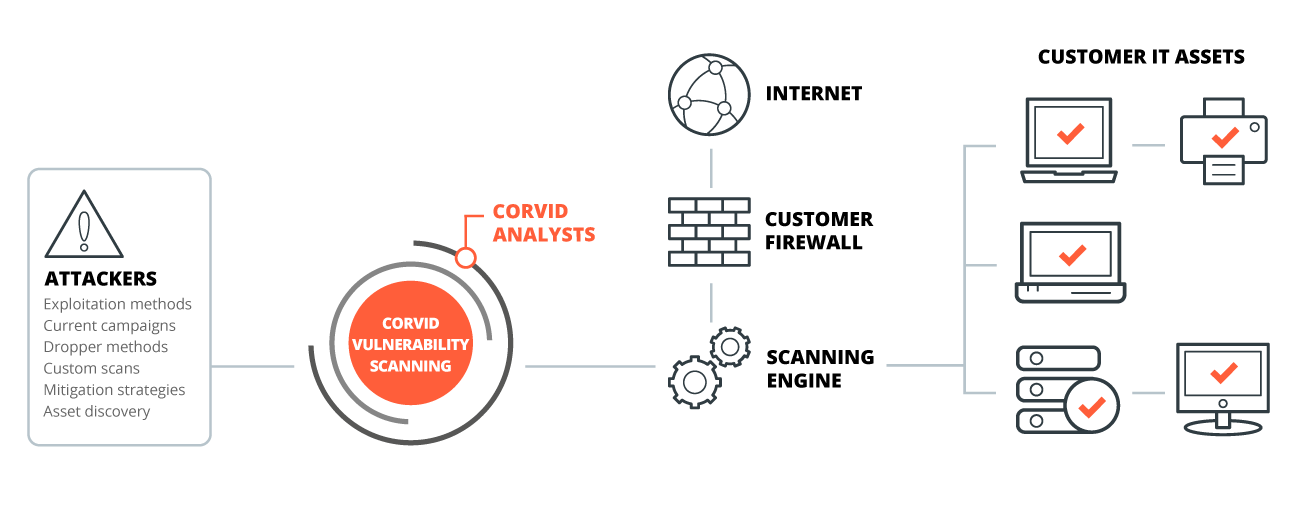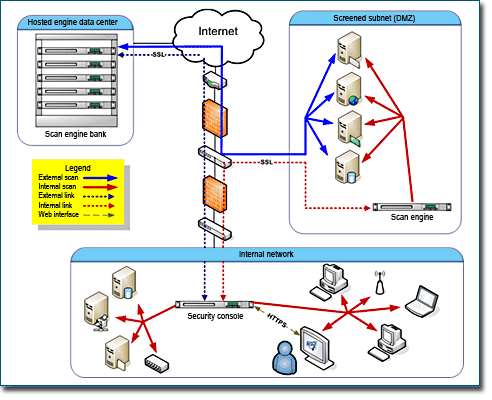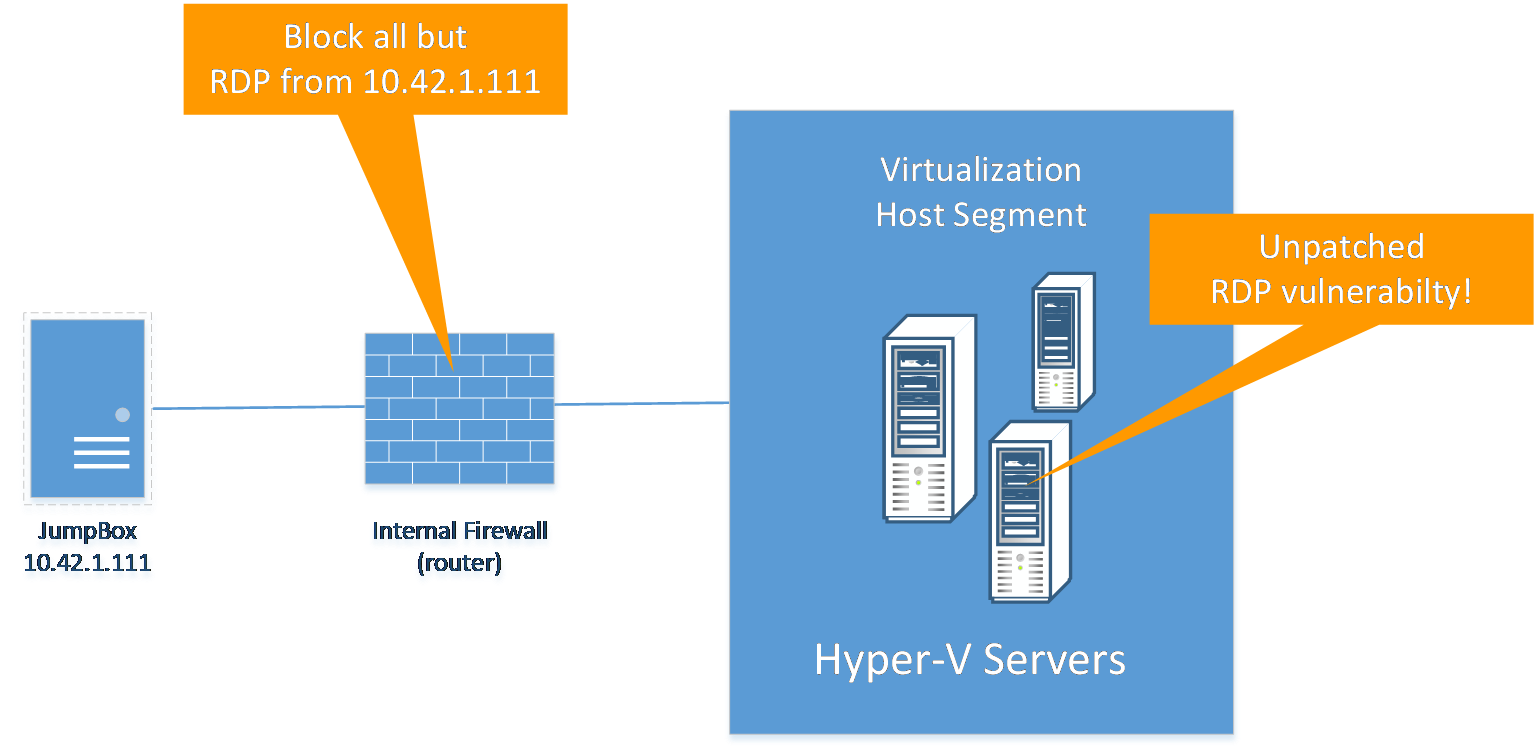
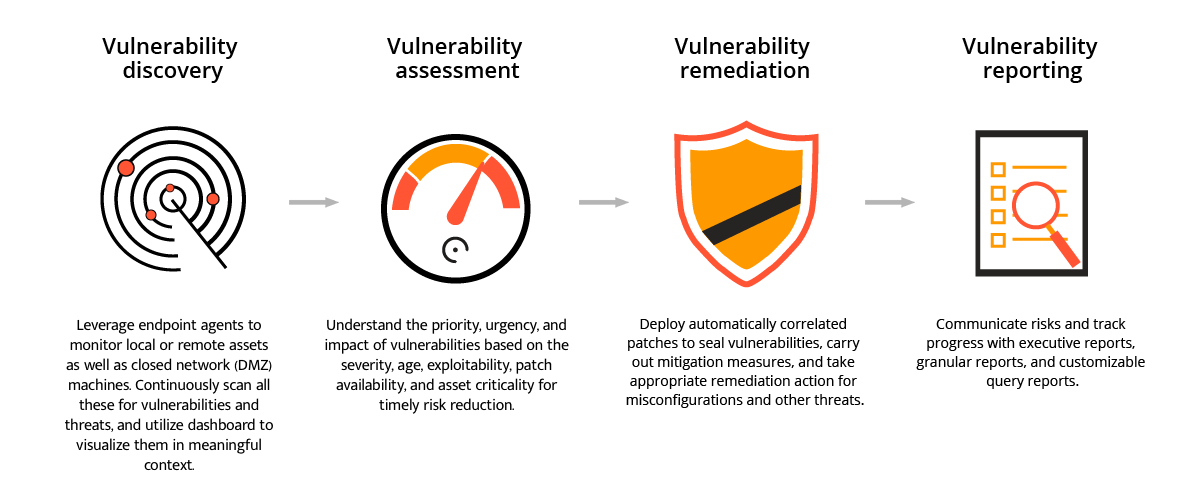
Correlating Vulnerability Scans with Network Path Analysis to Find and Remediate the Biggest Risks to Your Network and Avoid Wasting Time on the Little Ones
Vulnerability Scanner | Powerful Vulnerability Scanning Tools - ManageEngine Vulnerability Manager Plus

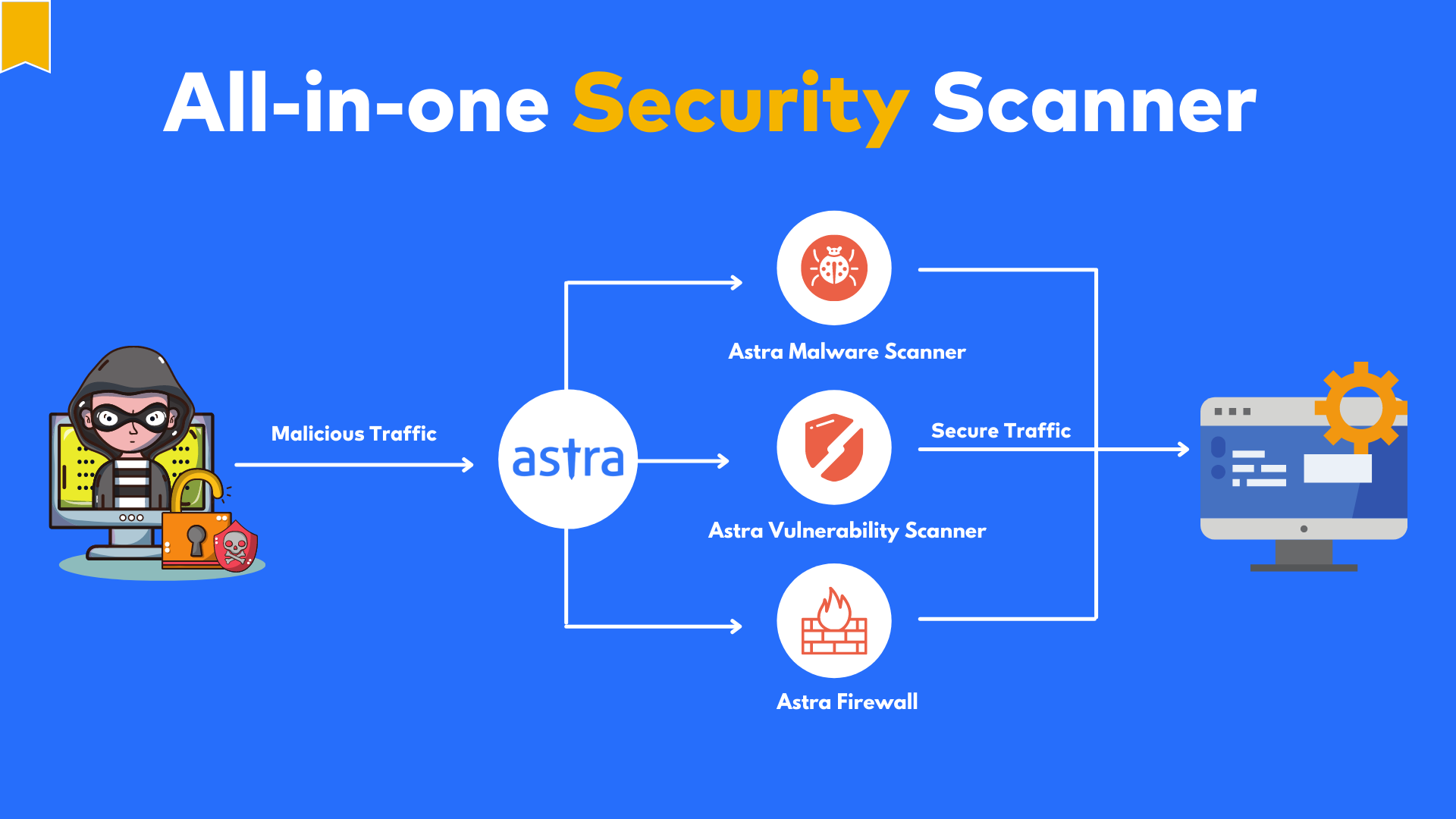
Premium Vector | Cyber or web security online service or platform set. digital data protection and database safety. online course, forum, firewall, vulnerability scanner. flat vector illustration